
How to Detect Shadow AI
A practical guide to detecting shadow AI across browser extensions, SWG endpoint agents, network telemetry, SaaS logs, endpoint agents, AI gateways, and MCP gateways.
Loading page...
Evergreen explainers, framework analyses, and deployment playbooks on AI red teaming, runtime guardrails, agent security, and Claude in production.

A practical guide to detecting shadow AI across browser extensions, SWG endpoint agents, network telemetry, SaaS logs, endpoint agents, AI gateways, and MCP gateways.

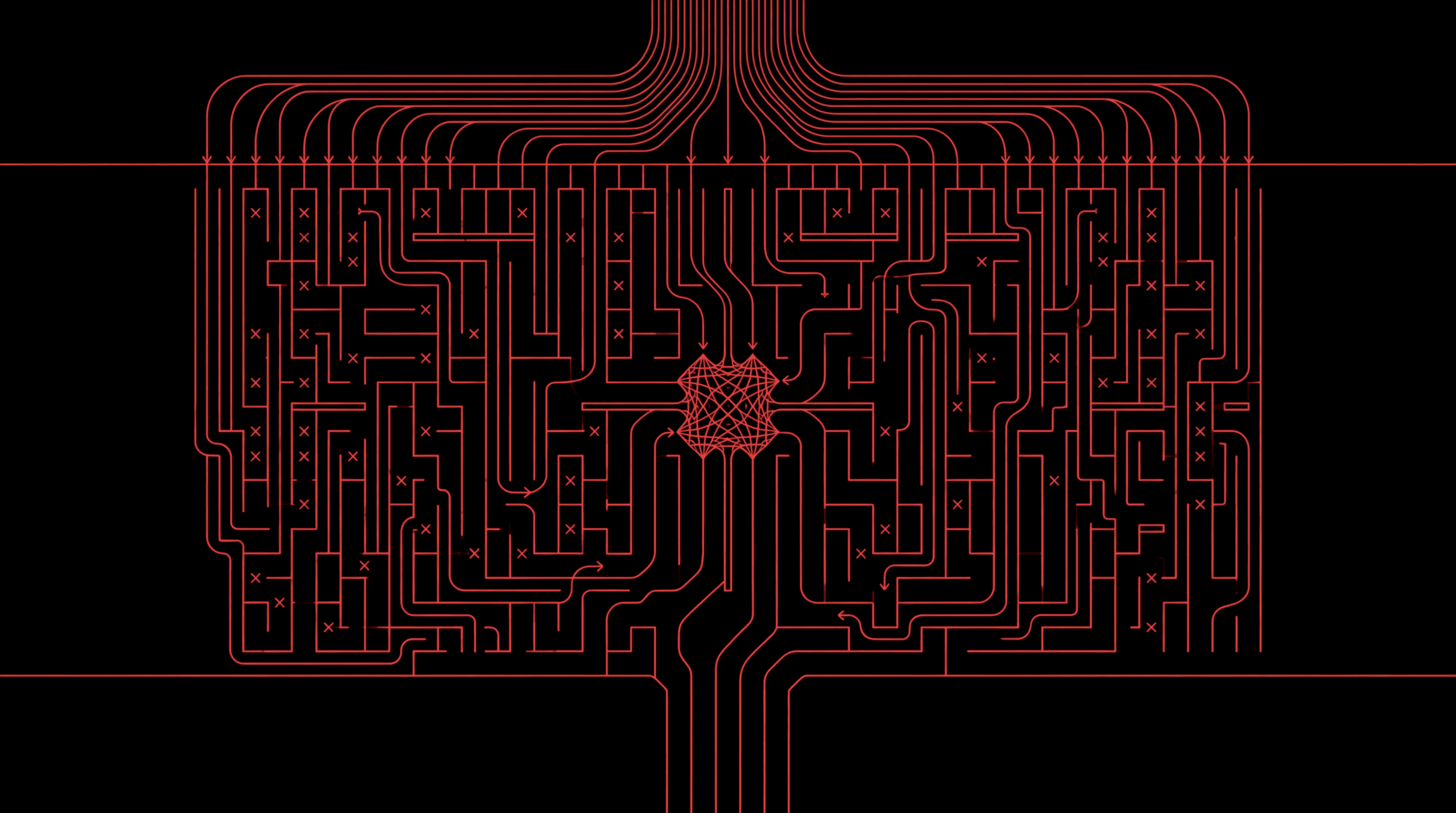
The Model Context Protocol expanded what AI agents can reach, and expanded the attack surface across at least nine distinct vectors. A primary-source threat model for MCP servers, with concrete controls, real CVEs, and the GA Supabase exploit walked end to end.

Claude Cowork and Claude Code share an agentic architecture but ship very different enterprise controls. A primary-source comparison of sandbox, network, audit-log, MCP, and decision-framework differences for security teams.

Anthropic shipped a Compliance API for Claude.ai and the Claude API. It exposes audit events and on-demand chat and file content, and it does not cover Claude Cowork. Here is what the API actually audits, what it misses, and how to assemble a complete audit story across the Compliance API, OpenTelemetry, and an on-device proxy.

Claude Cowork brings Claude Code-style agentic work to local files, browsers, apps, plugins, and scheduled tasks. Here is how to put a middleman proxy, browser controls, computer-use limits, and enterprise monitoring around it before using it on real work.

AI red teaming is adversarial testing of AI systems to find exploitable vulnerabilities before attackers do. Learn how it works, key techniques, real exploit examples, and how to implement it.

A complete guide to AI guardrails: what they are, the eight main types, how they work architecturally, and how to evaluate them for production LLM and agentic deployments.

An analytical guide to the OWASP Top 10 for Agentic Applications 2026: what the ten risks are, how they relate to each other, and what they imply for builders of agentic systems.
An analytical guide to the AI guardrails landscape: the architecture behind runtime safety, the ten tools that matter, what adversarial benchmarks actually show, and the decisions that determine whether guardrails hold under pressure.